From Floppy Disks to Ransomware: How Threats Shaped the Evolution of IT Security
Over the past four decades, information technology has transformed the way organizations operate. From early standalone computers to today’s globally connected cloud infrastructure, digital systems now support nearly every aspect of business. Yet alongside this growth has been the steady evolution of cyber threats. In many ways, the history of IT security is not simply a story of technological progress; it is a story of organizations adapting to an increasingly complex threat environment.
In the 1980s, computer security was relatively simple. Most systems operated independently or within small internal networks. Security focused primarily on physical access to machines and basic user permissions. Early computer viruses existed, but they were typically spread through floppy disks and were often created more as technical curiosities than as tools for profit or disruption. For most organizations, cybersecurity was not considered a strategic priority.
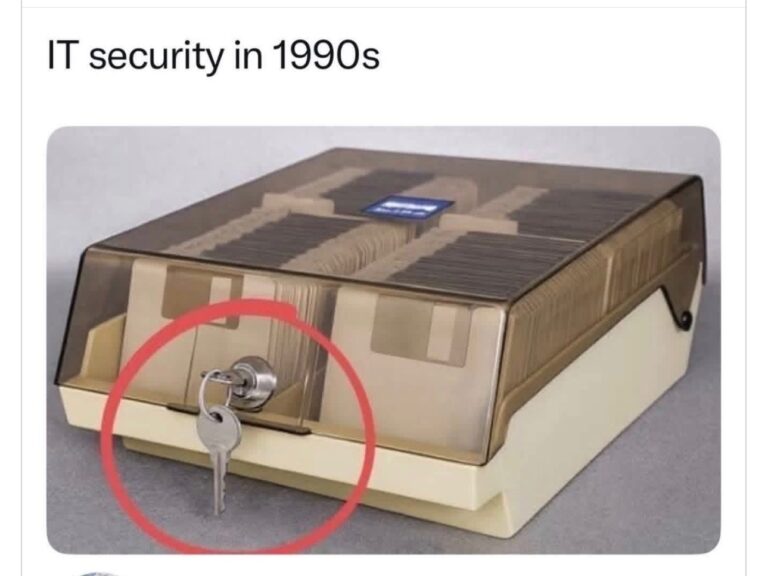
In the 1980s, computer security was relatively simple. Most systems operated independently or within small internal networks. Security focused primarily on physical access to machines and basic user permissions. Early computer viruses existed, but they were typically spread through floppy disks and were often created more as technical curiosities than as tools for profit or disruption. For most organizations, cybersecurity was not considered a strategic priority.
Things changed rapidly in the 1990s with the rise of the Internet. As businesses connected their internal systems to the global network, the threat expanded dramatically. Hackers were no longer limited by geography and could probe systems remotely for weaknesses. The emergence of network-based attacks drove the development of firewalls, intrusion detection systems, and more structured approaches to network security. Organizations began to recognize that protecting information required more than basic access controls; it required defensive architecture designed to monitor and defend entire networks.
The early 2000s brought another major shift as cybercrime evolved into a profitable, organized activity. High-profile worms and widespread malware outbreaks demonstrated how quickly vulnerabilities could be exploited globally. Phishing campaigns have become a common tactic, targeting employees directly rather than relying on technical defenses alone. These developments forced companies to expand their security strategies to include patch management, security awareness training, and layered defense models. Cybersecurity was no longer just a technical issue; it had become a business risk.
The following decade brought even greater complexity. The rapid adoption of cloud computing, mobile devices, and remote connectivity fundamentally changed how organizations manage and store data. The traditional concept of a secure network perimeter began to disappear as employees accessed corporate systems from homes, airports, and personal devices. At the same time, attackers grew more sophisticated. Ransomware attacks began targeting hospitals, municipalities, and private companies, often shutting down operations until payment was made. Large-scale data breaches exposed millions of customer records, reinforcing the importance of protecting both infrastructure and sensitive information.
Today’s cybersecurity landscape reflects this long evolution. Organizations operate in hybrid environments that combine in-house systems, cloud platforms, mobile devices, and third-party vendors. Threat actors use automation, credential theft, social engineering, and advanced malware to exploit both technical vulnerabilities and human behavior. In response, modern security strategies now emphasize identity management, multi-factor authentication, continuous monitoring, and incident response readiness.
One lesson has remained consistent throughout the past forty years: security evolves because the threat evolves. Each advancement in connectivity and technology has created new opportunities, but also new risks. The organizations that succeed in this environment are those that treat security as a continuous process rather than a one-time solution. The future of security will continue to be shaped by innovation—but also by the adversaries who seek to exploit it. Staying ahead requires vigilance, adaptability, and a commitment to building resilient systems that can withstand tomorrow’s threats.
At Teachout Security Solutions, we recognize that protecting organizations today requires a comprehensive approach. Physical security, personnel awareness, and technology protection are increasingly interconnected. As threats continue to evolve, so must the strategies used to defend against them. Understanding how we arrived at today’s cybersecurity landscape helps organizations better prepare for the challenges ahead.

