Author: Sarah Stedman

Homegrown Extremism Isn’t Solo: The Hidden Networks Behind ‘Lone’ Attacks
In recent months, federal authorities have disrupted multiple plots across the United States. These include the Halloween plot
Advice, Emergency Planning, Threat Assessment, Training Security Teams
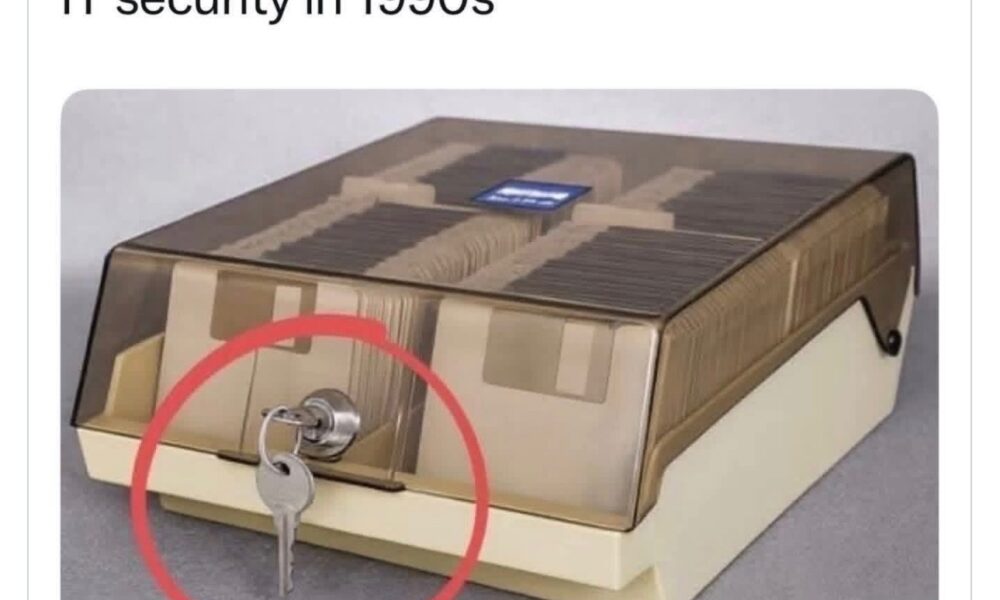
From Floppy Disks to Ransomware: How Threats Shaped the Evolution of IT Security
Over the past four decades, information technology has transformed the way organizations operate. From early

Advice, Emergency Planning, Threat Assessment, Training Security Teams
Threat Assessment: The 764 Network and Associated Online Extremist Communities
The 764 network and its affiliated subgroups represent one of the most serious and rapidly evolving online

